Seeing James Bond – Skyfall again allowed me to savor a film, which skilfully mocks Holywoodian clichés. One scene in particular is rich in teaching: Daniel Craig – archetype of the alpha male – is tied up by a Javier Bardem openly playing on his sexual ambiguity. Mentioning homosexuality in a blockbuster destined for the global market is an encouraging sign of a changing world. The playboy in the service of his Majesty finds himself in an awkward position trying to regain the psychological ascendancy. The wolf turned sheep is never more human in my opinion than at that time.

But beyond the refreshing acting game where glamor meets technological intrigue, several elements deserve our attention in cybersecurity. First of all, let’s get attached to the place in which James finds himself attached – namely the laboratory of Raoul Silva. A laboratory made up of a farm of servers exposed to the eyes and to the sight of all on a deserted island. Realistic? Not really ; but is it very important ? Nothing is less sure.
Note instead that exhibiting a battery of capricious machines in a dusty room open to the four winds is seldom a good idea. Furthermore if this installation is combined with a power supply dating from the former USSR not very conducive to being secured and redundant as it should be. Let’s also go over the red lights to witness the evil calculations that are at work. Let us simply note that the readers working in outsourcing would pass for geniuses if we had to compare their protective measures against this installation. And no matter what the gossip, OVH engineers have nothing to learn on the subject. On the contrary, reality blithely exceeds fiction.
However, this is not the element on which I wish to dwell on. By far the most questionable element is the speech about the speed and immediacy of villainous Silva’s computer attacks.
Often to punctuate the action when it is not simply to provide an obscure explanation for a flawed plot, computer attacks appear as the work of little genius that manages to break into systems after only a few hours.
The reality in terms of human organization and the attack process would not be further away. This process, called the cyber-kill chain, defines the life cycle of a standard cyber attack. That is to say the different phases of an intrusion into a computer system. While there are many interpretations of this chain, the most basic form consists of seven stages whose modalities are richer, more resourceful, and with more twists and turns than big-budget movies attempting to replicate it.
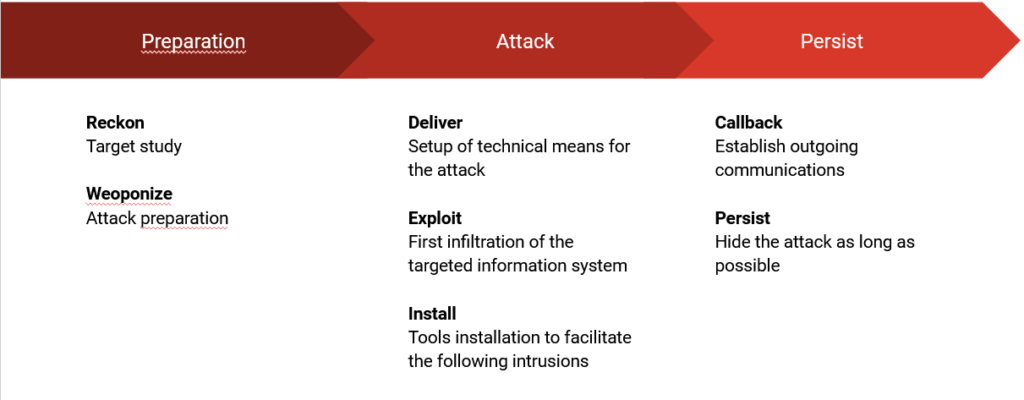
Let us detail for these 7 stages, the plurality of scenarios and consequences that they imply.
Reckon
The recognition or information gathering phase aims, as its name suggests, to collect as much information as possible on the intended target. Unlike James Bond blithely sticking his head in the lion’s mouth, a motivated attacker primarily favors external data sources to avoid any contact with the target. The less direct contact between the attacker and the target, the less chance there is of being detected. For this reason, attackers will delay direct contact with their target until it is time to strike.
Open source intelligence (OSINT) is intelligence obtained by a public information source. Instagram, Facebook and Linkedin are often gold mines for retrieving information allowing the profile of the chosen target to be drawn up. Attackers can thus spend months gathering information about a target to maximize their chance of success.
Is social engineering just for amateurs?
Surely you think that system administrators are aware of the security issues they address on a daily basis? Most of the time, this is the case. Yet it is not uncommon for leaks of sensitive information to inadvertently end up on public cloud services. For example, a study by North Carolina State University (NCSU) reveals that more than 100,000 accounts on Github, the world’s leading code-sharing platform, contained sensitive identification data.
With a list of e-mails and usernames retrieved from poorly looking forums, an attacker is able to search for the corresponding online services. The tendency of many users to reuse passwords across multiple services drastically increases the likelihood of breaches. Penetrating the digital identity of a target through even a smaller digital service will allow the attacker to more easily ascend to critical services and information.
If you are interested in the subject of OSINT, I recommend reading this article presenting the main tools in this area.
Weaponize
After performing a thorough reconnaissance of a target, an attacker will have a better idea of where and how to strike.
In the militarization phase, the hacker builds his “cyber weapons” and prepares to strike the target. If the attack involves the deployment of malware, it must be hosted on a platform unrelated to the hacker. Likewise, if the attack involves phishing emails, the attacker will have to create the contents of the emails. This phase will be all the more relevant thanks to the information gathered during the reconnaissance phase to facilitate targeting of the target.
Despite greatly conditioning the success or failure of the following steps, this stage is hardly ever brought to light in the films because it constitutes a shadow work. Done well, it allows to identify the most conducive scenarios to the success of the attack.
Creating phishing pages to simulate real web portals or building servers to host malware are all necessary actions when preparing for the attack. Using tools like Puppet or Ansible to automate theirs actions, attackers host theirs infrastuctures on generic cloud resources like for exemple Google Cloud Platform. This has the advantage of considerably increasing their resilience against infrastructure dismantling.
Unlike a Raoul Silva in James Bond centralizing his servers on his island, it is smarter to disseminate his servers in the cloud in order to make them less vulnerable to dismantling.
Hosting on a trusted cloud like Google has the added benefit of providing a trusted domain. Traditional firewalls generally will not block this type of traffic. This configuration phase is therefore a pragmatic mix of resources to be implemented to adapt to the human, geographic and technical characteristics of the target. The unique model, as sophisticated as it may be, will always be less effective than a personalized approach based on a solid prior analysis.
Deliver
The attack really begins at this step.
During the delivery phase, the attacker aims to deliver the malicious payload to the targeted victim. This delivery can take the form of a phishing email, an infested website or even an abandoned USB drive.
The spread of cloud services has seen popular services like Pinterest and Instagram serve as a medium to spread viruses or a mean of infesting target. The use of provider recognized by the general public such as Google Drive promotes digital trust to fool the target. Generally speaking, the variety of delivery methods is limited to the imagination of its attackers.
Exploit
Unlike the devastating effects shown on the big screen, attacks are mostly invisible. Either they fail blocked by a security mechanism (firewall, etc.), or they succeed and aim to hide themselves as quickly as possible from their victims.
During the exploitation phase, the attacker will exploit the vulnerabilities found during the recognition phase, whether human or technical. For example, a contaminated web portal will redirect the user to a forged login form to steal their credentials.
This step may seem random but due to the number of unpatched systems in nature and new security vulnerabilities discovered every day, it is not uncommon for an attacker to have several vulnerabilities present on the same system. The stake for the attacker is to exploit the most undetectable flaw by the defense systems while guaranteeing the widest accesses in the target system. Regardless, the attackers aim to remain in hiding as long as possible in order to proceed with the next steps.
Install
Once the initial exploit happened, the attacker will start installing a series of utilities in order to gather additional information about the system. These will allow the attacker to infest the various remaining layers of the information system.
This is not because part of the information system has been hacked that all the systems are contaminated. Most of the time, the compromise only concerns a minor application that is less protected because it is of less importance for the company.
The install phase will thus allow the attacker to better understand the technical architecture of the systems from an internal point of view. Once again, blockbusters show compromises bringing the entire company to its knees where the hacker most often finds itself in a dead end with limited access (and information).
Callback
Penetrating an information system is not of much use if it is impossible to extract marketable information from it. As seen, attacks are long-term processes that can last for several months. However, the longer an attack, the greater the risk of being exposed. Reconciling sensitive data outside the contaminated information system can alert the defense mechanisms (IDS etc.).
When the malicious payload must send this information back to attackers, the challenge for attackers will be to mask this flow (thanks in particular to steganography – the exciting art of concealment) so that data theft is not detected by the host system.
Once again, using popular services like Google or Microsoft Azure allows malicious traffic to bypass firewalls and has the benefit of blending into regular traffic. This makes the requests detection more difficult but not impossible.
Persist
Most attackers don’t just pack up once the attack is successful. This is explained by the investment in time and money that an attack on a large target requires. The last phase consists in the implementation of a persistence mechanism to maximize long-term gains.
The longer an attack remains invisible, the greater the chances of maximizing gains. Once an anchor point has been established in a host system, attackers can notably attempt lateral movement in the company network or its partners. It is indeed easier to attack a third party system when one is part of a network already authorized to communicate with the target.
To hide in the crowd as long as possible…
… this could be the leitmotif of attackers using the cyberkill chain! No step is obligatory in itself but their whole summarizes well the methodology employed by the attackers nowadays.
The industrialization of the attacks and their necessary cover-ups don’t fit well with the brilliant actions staged in James Bond. To be effective, egos must give way to the concealment of actions.
“Patience and length of time, Are more than strength or rage.”
La Fontaine – The Lion and the Rat
